Bad Browser Plug-ins Gone Wild: Malvertising, Data Exfiltration
Por um escritor misterioso
Descrição
This post was authored by Fred Concklin, William Largent, Martin Rehak, Michal Svoboda, and Veronica Valeros. During an average day of surfing the web via computer, smartphones, and tablets, we
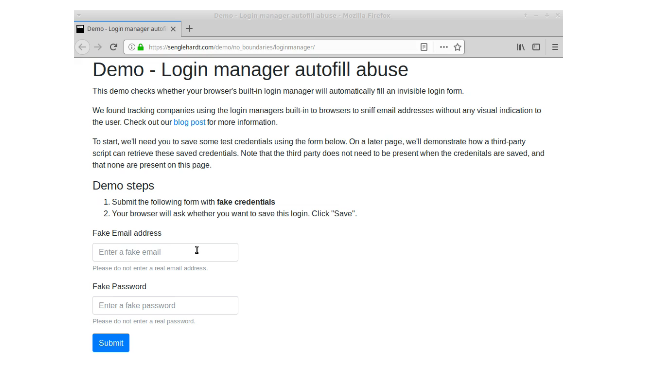
No boundaries for user identities: Web trackers exploit browser login managers - Freedom to Tinker

PrivateLoader: network-based indicators of compromise
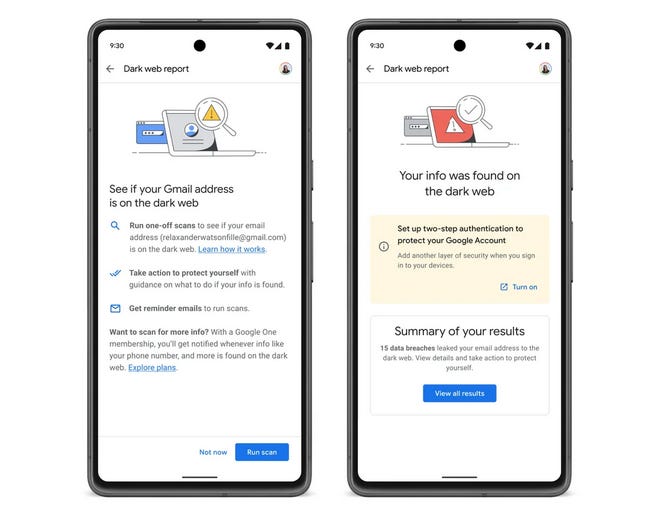
Risky Biz News: Gmail will warn users when their email address appears on the dark web
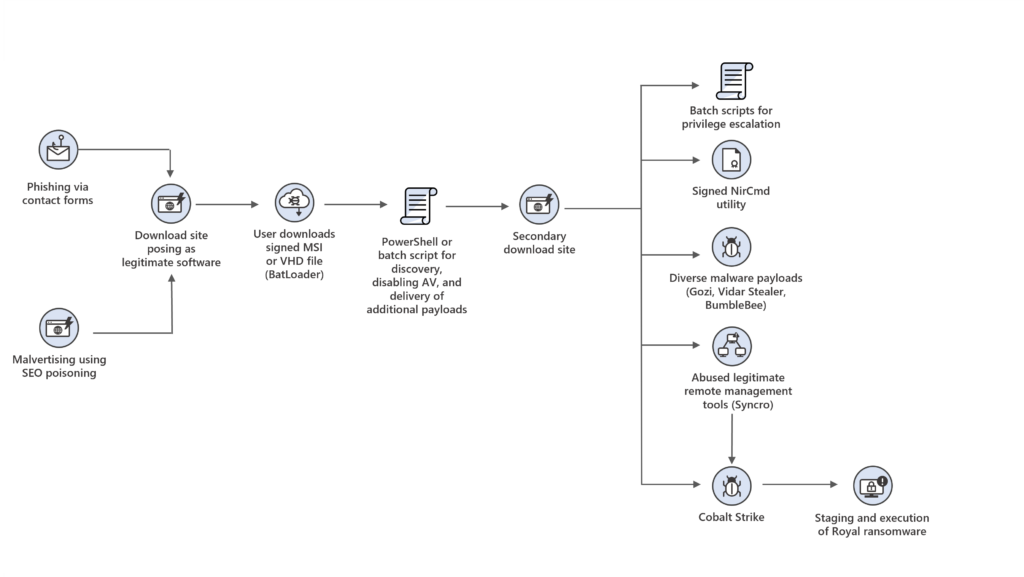
Swedish Windows Security User Group » phishing
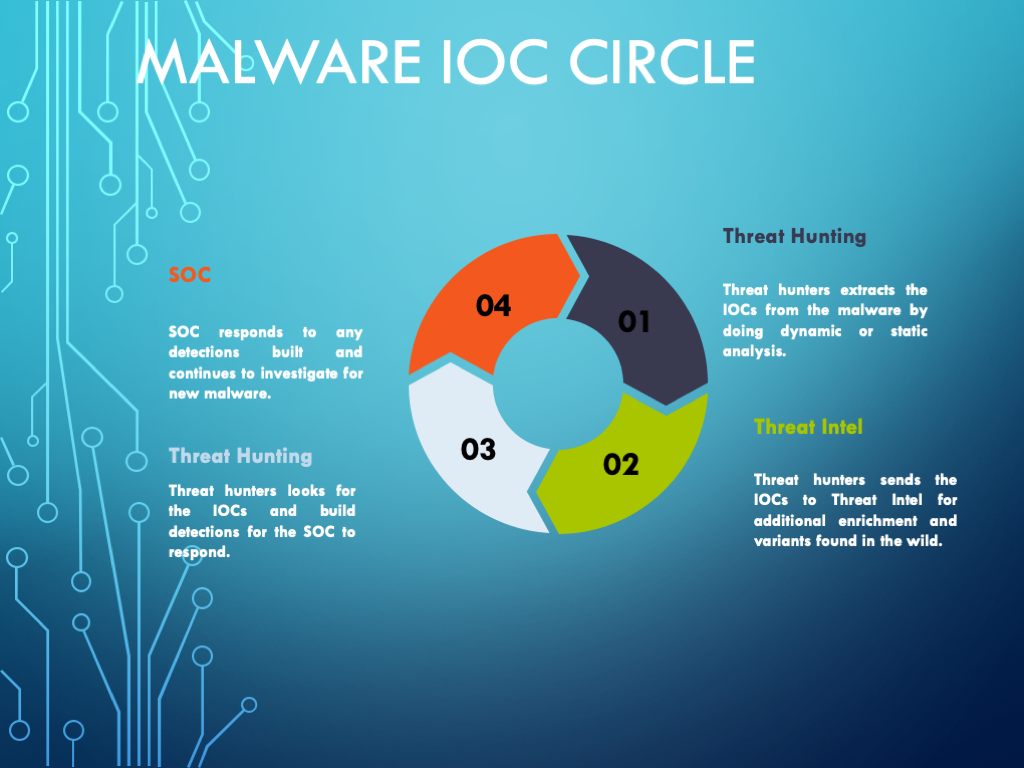
Malware Analysis Framework v1.0
Our Blog
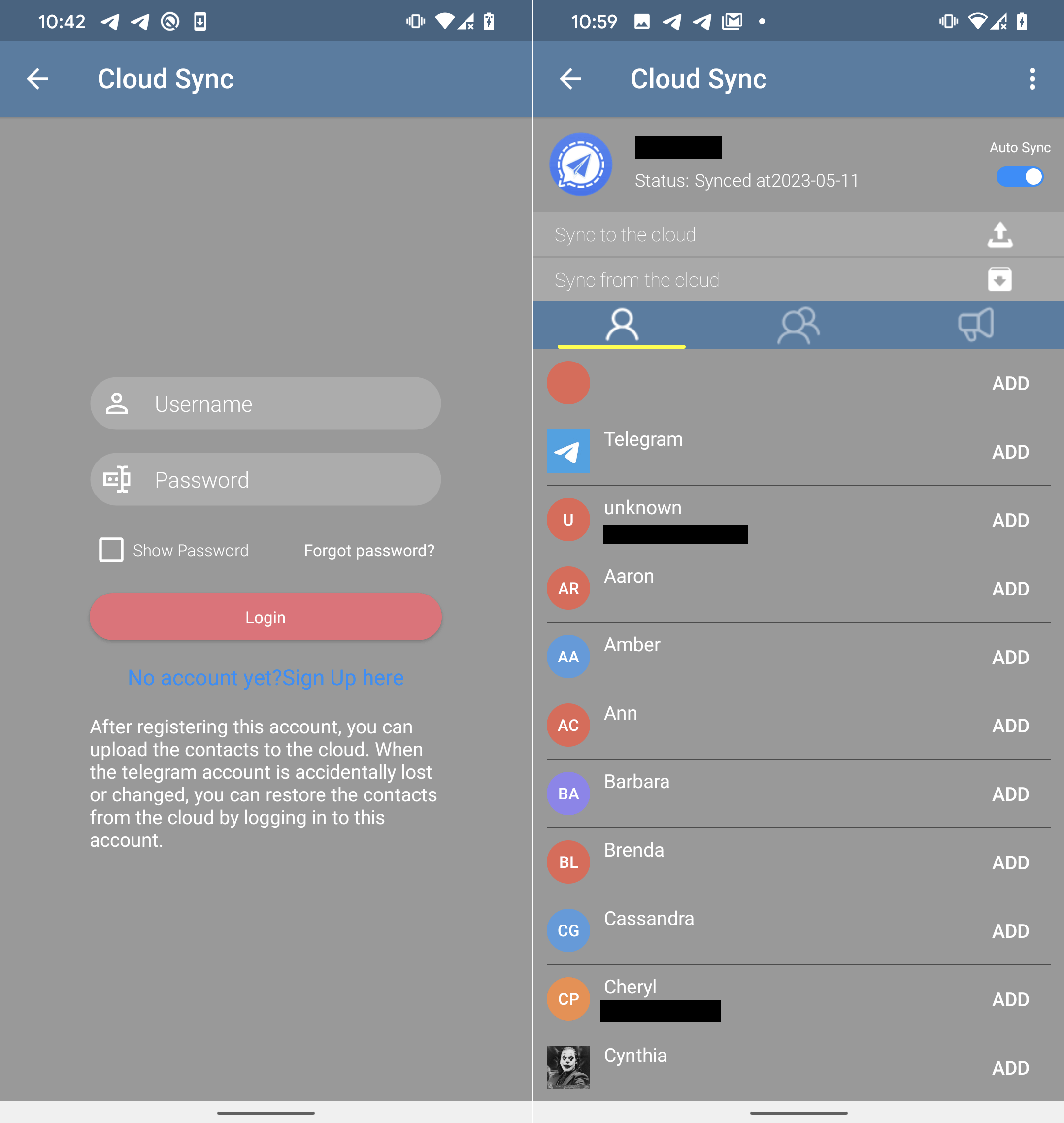
BadBazaar espionage tool targets Android users via trojanized Signal and Telegram apps

Quick off the blocks: Darktrace AI detects Egregor ransomware attack on day one of deployment
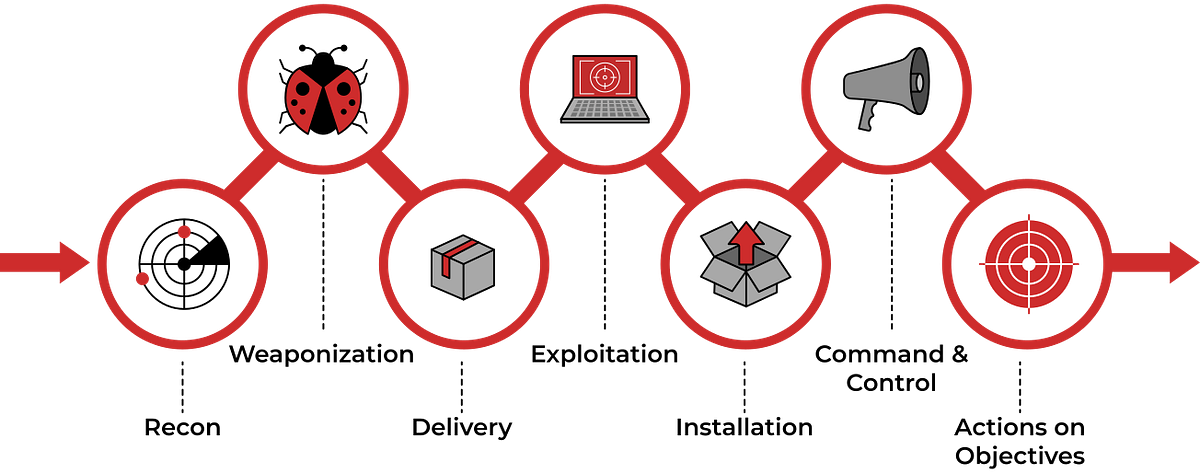
TryHackMe Cyber Kill Chain Room. The Cyber Kill Chain framework is…, by Haircutfish
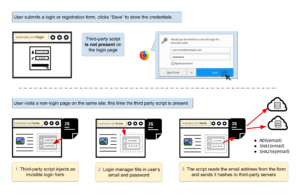
No boundaries for user identities: Web trackers exploit browser login managers - Freedom to Tinker

Cyware Weekly Threat Intelligence, July 17-21, 2023
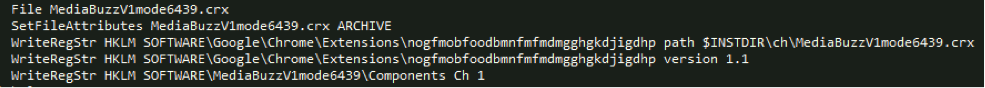
Bad Browser Plug-ins Gone Wild: Malvertising, Data Exfiltration, and Malware, Oh my! - Cisco Blogs
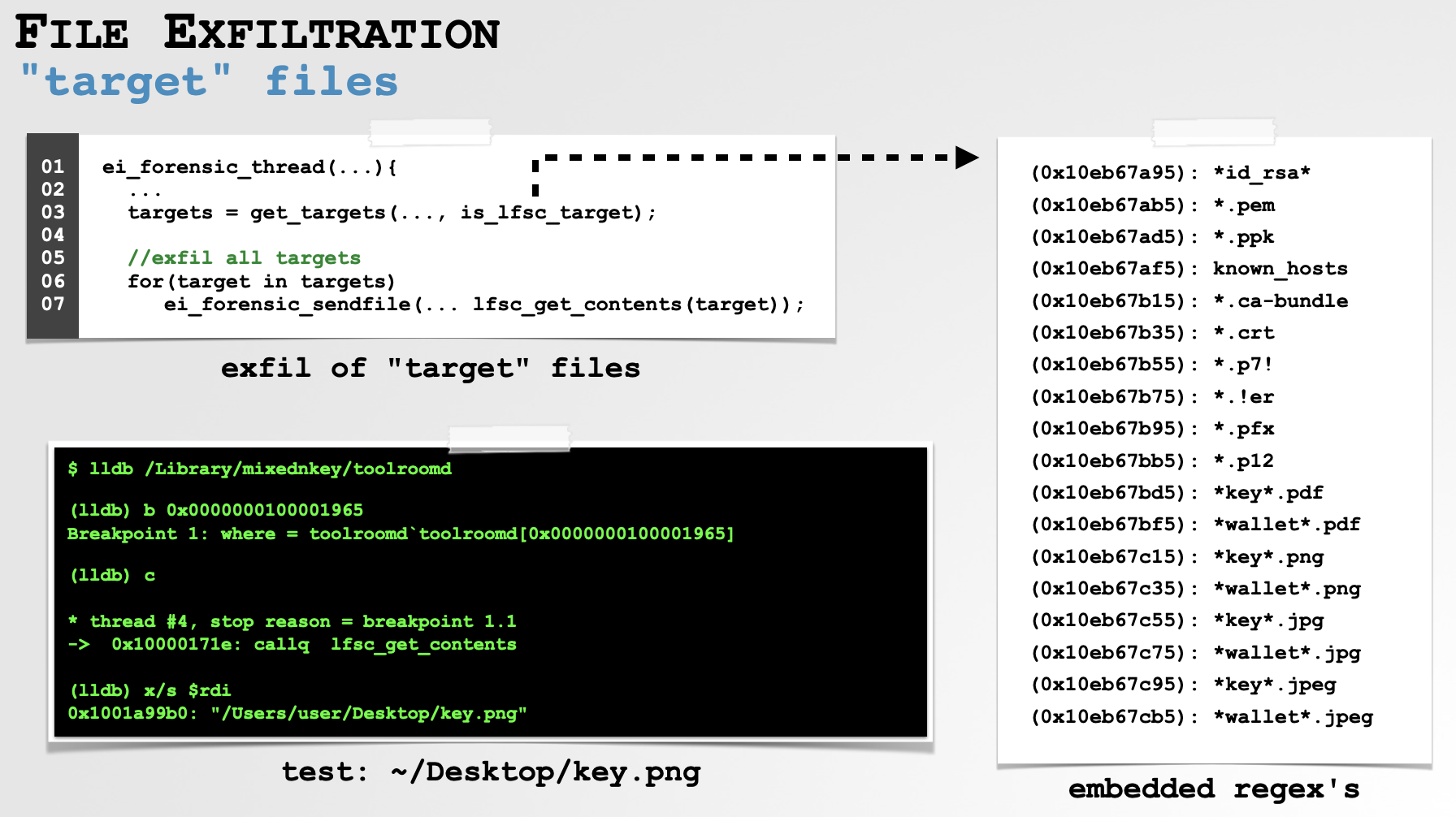
Objective-See's Blog
de
por adulto (o preço varia de acordo com o tamanho do grupo)







