What Is Screen Hacking and How To Avoid It - IDStrong
Por um escritor misterioso
Descrição
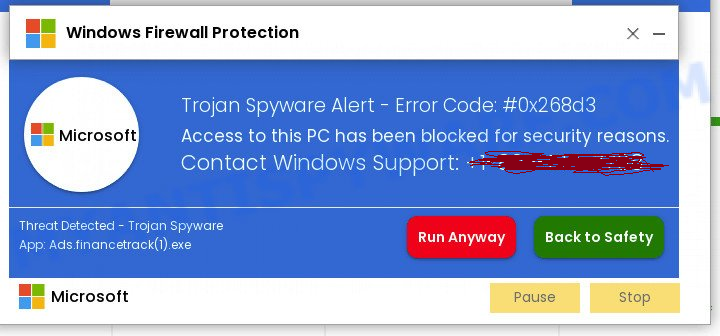
Screen hacking is a type of contactless attack that involves taking control of a user’s smartphone or computer touchscreen using electromagnetic interference.

Hacker's Hands Typing Malicious Code Into Stock Footage SBV

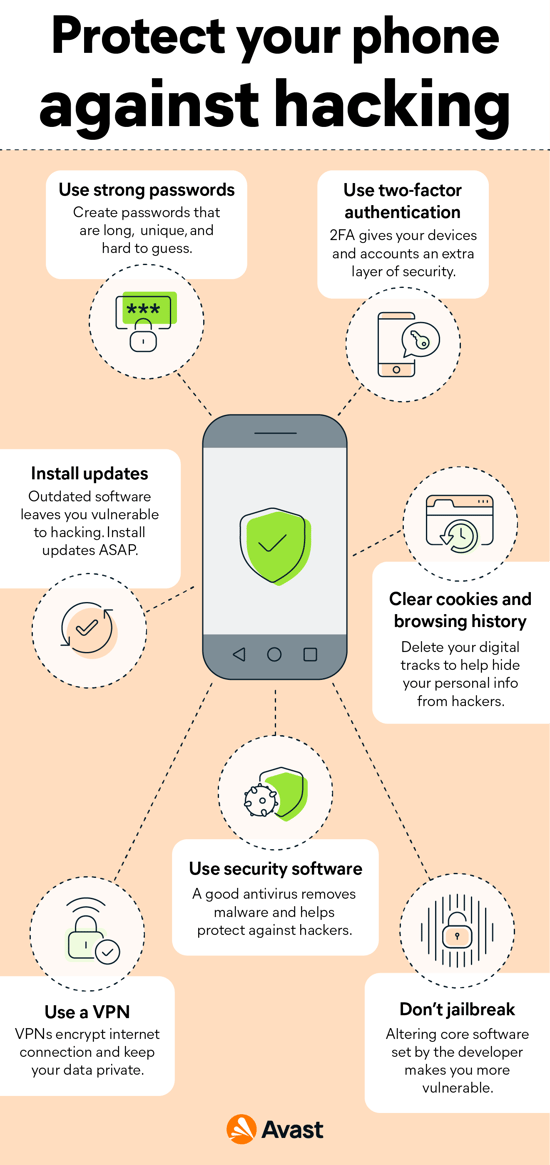
6 Ways You Can Protect Yourself From Hacking
10 Signs That Your Phone Has Been Hacked
Hacking Exposed - Linux.pdf - Department of Electrical Engineering
Signs Your Phone Has Been Hacked
Old Attacks Made New Again by Hackers Exploiting our Browsers and

Bluebugging Attack: Definition and Prevention - IDStrong

Accessing the dark web is easier than you think. #darkweb

What Is Screen Hacking and How Can You Protect Yourself?

What are White Hat, Black Hat, and Gray Hat Hackers

Credential Stuffing: Definition and Prevention - IDStrong

Major data breaches this week. Try a free identity threat scan at
What are the ways to protect your identity from hackers? - Quora

How to Prevent Hacking: 15 Proven Tricks to Avoid Hacking

Kids Hacking iOS Screen Time
de
por adulto (o preço varia de acordo com o tamanho do grupo)